Data sharing is increasingly battling data-privacy concerns in an AI-dominated business society. As a result, organizations must be exceedingly cautious with any private, sensitive, or confidential data in the approaching era of data protection laws. Simultaneously, it is vital to exchange and collaborate data to stimulate innovation and discovery.
As enterprises make inroads into data-intensive AI applications, these multiple and sometimes contradictory objectives will become even more imperative. Organizations are not alone as they struggle to negotiate the twists and turns in the path to data sharing while maintaining data privacy. Many corporations and research organizations are working to assist them in addressing the difficulties at hand — and paving the way for a future in which data sharing does not conflict with data-privacy concerns.
Read more: 5 Ways Today’s Workplace Has Transitioned Digitally
Security concerns associated with Data Sharing
External sources listening on the network, unauthorized users, and internal users handing out the store endanger the integrity and privacy of data. This section describes the potentially dangerous conditions and assaults that could compromise your data.
- Accidental Exposure – Many data breaches are consequences of negligence or exposure of sensitive data rather than a deliberate attempt. Employees in an organization frequently share, grant access, lose or mishandle valuable data, either accidentally or because they are unaware of security standards.
- Data Tampering – With distributed setups comes the prospect that a malevolent third party can commit a computer crime by tampering with data as it passes between sites.
- Eavesdropping and Data Theft – On the internet and Wide Area Network (WAN) environments, public carriers and private network owners frequently route their networks via insecure landlines, vulnerable microwave and satellite connections, or several servers. These tend to expose valuable data to any external party.
- Ransomware – Ransomware is a significant threat to data. Ransomware is a virus that infects corporate devices and encrypts data, rendering it unusable without the decryption key.
- Falsifying User Identities – Criminals steal users’ credit card numbers and then use them to make purchases on their accounts. Or they steal additional personal information such as checking account numbers and driver’s license numbers and use it to open phony credit accounts in the name of someone else.
- Accountability – If the system administrator cannot trace user activities, users cannot be held accountable for their actions.
- Complex User Management Requirements – The complexity of handling user accounts and passwords in large-scale environments leaves your system exposed to errors and attacks.
Read more: Why is It Necessary to Safeguard Data Privacy in Project Management?
Data Sharing Security – Why it matters?
According to the Ponemon Institute’s Cost of Data Breach Study, the average cost of a data breach in the United States is $8 million. Furthermore, a data breach affected a total of 25,575 user accounts, meaning that, in addition to financial losses, such occurrences lead to a loss of customer trust and a damaged reputation.
Almost everyone in the consumer goods sector understands that poor brand experiences can swiftly undo years of brand building, a hard-earned favorable reputation, and perhaps most significantly, the trust a customer places in a brand. In today’s age of big data and digital marketing, where consumer goods businesses and merchants build detailed profiles of individual consumers based on data sources, a single data breach can significantly undermine consumer trust.
Winning consumers’ trust will be critical in the future when customer data will be a source of competitive advantage. Companies open and honest about their data usage have the opportunity to win confidence. According to Gartner, firms who successfully build digital trust will engage in 50% more ecosystems, extending revenue generation by 2023.
Businesses must transition to a mutually advantageous data approach that gives customers greater control and gives them authorization for direct access to high-quality data in return for improved, hyper-personalized solutions with enhanced security and privacy. For this, management must develop a culture, train executives, change its organizational architecture and operating model, and evolve skills, technology, and procedures to improve how customers interact with the company and its goods at every touchpoint.
Read more: All You Need to Know About Dashboards and Data Security
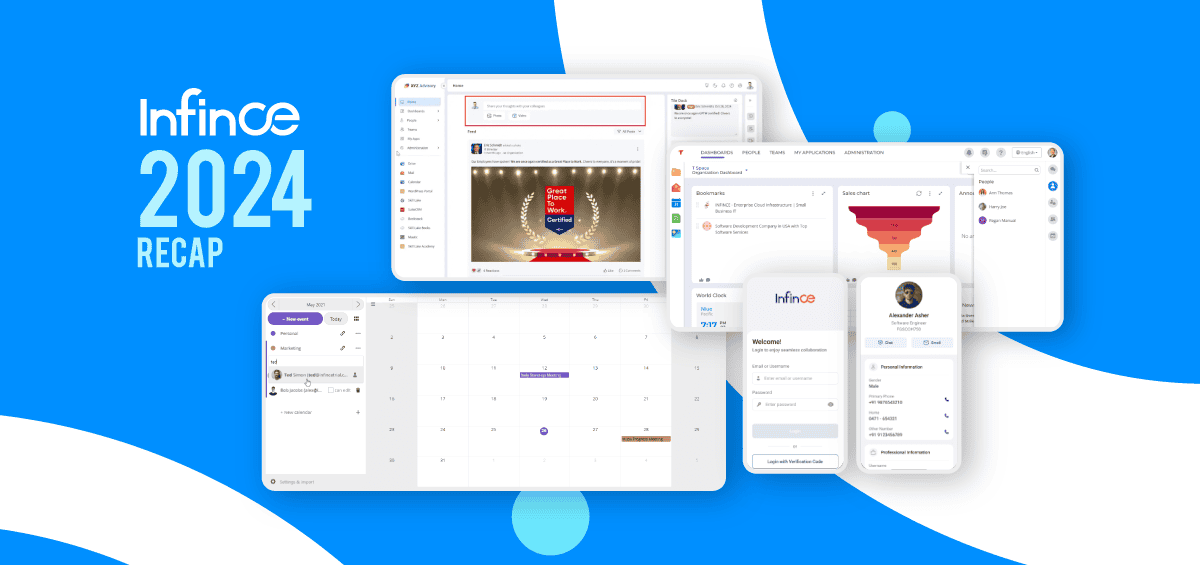
How Infince helps to boost Customer Trust
At Infince, we see data privacy and security as more than just a risk management issue; but as a possible strategic asset that can be a component of brand building and company reputation. When you subscribe to Infince, your valuable data is kept on a virtual private server that is accessible only by your organization. You may safely access your data from anywhere from across the globe through an internet-connected device. Except for the files you download, all data is stored on Infince and cannot get saved to a user’s computer. As a result, you get to broaden your business with Infince to achieve process improvements, cost reductions, rapid business growth, and, most importantly, increased customer trust.
Some interesting features of Infince include:
- Customizable Dashboards
- Collaboration Apps
- Branded Mobile App
- Business Phone System
- Domain Registration
- Productivity Tools
- Curated Application Marketplace
- Virtual Private Server
- Server and Storage Monitoring
Infince’s comprehensive approach, based on numerous layers of security that contribute to increased consumer trust, includes:
- Improved Data Security – Enjoy complete data privacy by utilizing virtual private servers, firewalls, and encryption/password-based access controls.
- Concierge Support – You get to use concierge support via email, phone, and live chat to assist firms in planning and deploying the best technology solutions to streamline operations.
- Device Independence – Access the business management software from anywhere using any device and resume where you left off.
- Easy Scalability – Scale effortlessly as your business grows by expanding server capacity and storage space without incurring additional expenditures.
- Simplified IT Management – Build from the ground up, upgrade existing programs, or interface with your existing systems using a unified platform.
Need assistance determining how to keep your data secure regardless of what? Talk to our experts for a quick tour of the Infince platform.